|
Mbed TLS v4.0.0
|
|
Mbed TLS v4.0.0
|
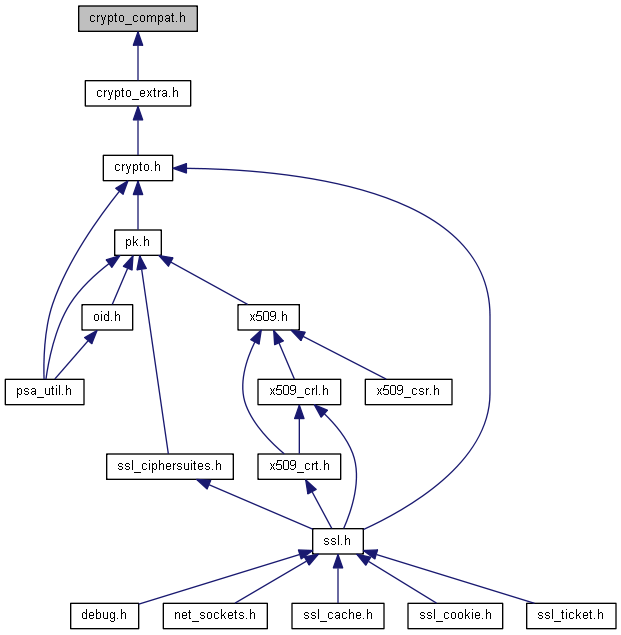
PSA cryptography module: Backward compatibility aliases. More...
Go to the source code of this file.
Macros | |
| #define | PSA_KEY_TYPE_DES ((psa_key_type_t) 0x2301) |
| #define | PSA_ALG_JPAKE_BETA PSA_ALG_JPAKE_BASE |
Functions | |
| int | psa_can_do_hash (psa_algorithm_t hash_alg) |
PSA cryptography module: Backward compatibility aliases.
This header declares alternative names for macro and functions. New application code should not use these names. These names may be removed in a future version of Mbed TLS.
Definition in file crypto_compat.h.
| #define PSA_ALG_JPAKE_BETA PSA_ALG_JPAKE_BASE |
The beta encoding of JPAKE algorithms, with no hash.
This came from the beta version of the PSA Crypto PAKE 1.2 extension, which is what Mbed TLS 3.x implemented. Since TF-PSA-Crypto 1.0.0, we no longer support the beta version of specification, so this algorithm encoding is no longer supported in JPAKE cipher suites. Use PSA_ALG_JPAKE instead.
Definition at line 60 of file crypto_compat.h.
| #define PSA_KEY_TYPE_DES ((psa_key_type_t) 0x2301) |
Definition at line 43 of file crypto_compat.h.
| int psa_can_do_hash | ( | psa_algorithm_t | hash_alg | ) |
 1.8.6
1.8.6