This file provides an API for the RSA public-key cryptosystem. More...
#include "mbedtls/private_access.h"#include "mbedtls/build_info.h"#include "mbedtls/bignum.h"#include "mbedtls/md.h"#include "mbedtls/threading.h"#include "rsa_alt.h"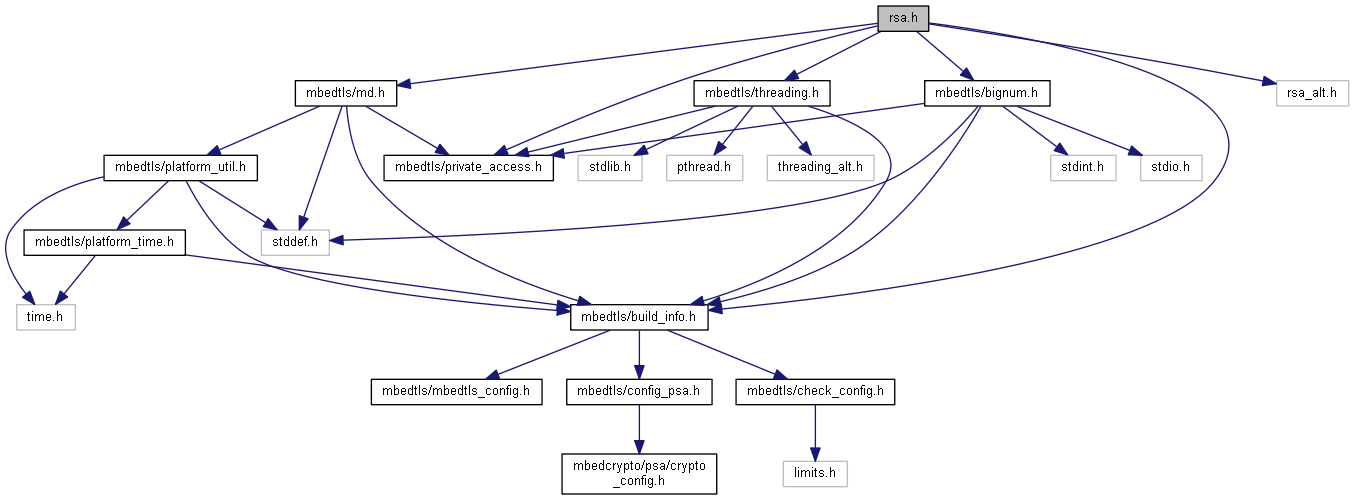
Go to the source code of this file.
Macros | |
| #define | MBEDTLS_ERR_RSA_BAD_INPUT_DATA -0x4080 |
| #define | MBEDTLS_ERR_RSA_INVALID_PADDING -0x4100 |
| #define | MBEDTLS_ERR_RSA_KEY_GEN_FAILED -0x4180 |
| #define | MBEDTLS_ERR_RSA_KEY_CHECK_FAILED -0x4200 |
| #define | MBEDTLS_ERR_RSA_PUBLIC_FAILED -0x4280 |
| #define | MBEDTLS_ERR_RSA_PRIVATE_FAILED -0x4300 |
| #define | MBEDTLS_ERR_RSA_VERIFY_FAILED -0x4380 |
| #define | MBEDTLS_ERR_RSA_OUTPUT_TOO_LARGE -0x4400 |
| #define | MBEDTLS_ERR_RSA_RNG_FAILED -0x4480 |
| #define | MBEDTLS_RSA_PKCS_V15 0 |
| #define | MBEDTLS_RSA_PKCS_V21 1 |
| #define | MBEDTLS_RSA_SIGN 1 |
| #define | MBEDTLS_RSA_CRYPT 2 |
| #define | MBEDTLS_RSA_SALT_LEN_ANY -1 |
Functions | |
| void | mbedtls_rsa_init (mbedtls_rsa_context *ctx) |
| This function initializes an RSA context. More... | |
| int | mbedtls_rsa_set_padding (mbedtls_rsa_context *ctx, int padding, mbedtls_md_type_t hash_id) |
| This function sets padding for an already initialized RSA context. More... | |
| int | mbedtls_rsa_import (mbedtls_rsa_context *ctx, const mbedtls_mpi *N, const mbedtls_mpi *P, const mbedtls_mpi *Q, const mbedtls_mpi *D, const mbedtls_mpi *E) |
| This function imports a set of core parameters into an RSA context. More... | |
| int | mbedtls_rsa_import_raw (mbedtls_rsa_context *ctx, unsigned char const *N, size_t N_len, unsigned char const *P, size_t P_len, unsigned char const *Q, size_t Q_len, unsigned char const *D, size_t D_len, unsigned char const *E, size_t E_len) |
| This function imports core RSA parameters, in raw big-endian binary format, into an RSA context. More... | |
| int | mbedtls_rsa_complete (mbedtls_rsa_context *ctx) |
| This function completes an RSA context from a set of imported core parameters. More... | |
| int | mbedtls_rsa_export (const mbedtls_rsa_context *ctx, mbedtls_mpi *N, mbedtls_mpi *P, mbedtls_mpi *Q, mbedtls_mpi *D, mbedtls_mpi *E) |
| This function exports the core parameters of an RSA key. More... | |
| int | mbedtls_rsa_export_raw (const mbedtls_rsa_context *ctx, unsigned char *N, size_t N_len, unsigned char *P, size_t P_len, unsigned char *Q, size_t Q_len, unsigned char *D, size_t D_len, unsigned char *E, size_t E_len) |
| This function exports core parameters of an RSA key in raw big-endian binary format. More... | |
| int | mbedtls_rsa_export_crt (const mbedtls_rsa_context *ctx, mbedtls_mpi *DP, mbedtls_mpi *DQ, mbedtls_mpi *QP) |
| This function exports CRT parameters of a private RSA key. More... | |
| size_t | mbedtls_rsa_get_len (const mbedtls_rsa_context *ctx) |
| This function retrieves the length of RSA modulus in Bytes. More... | |
| int | mbedtls_rsa_gen_key (mbedtls_rsa_context *ctx, int(*f_rng)(void *, unsigned char *, size_t), void *p_rng, unsigned int nbits, int exponent) |
| This function generates an RSA keypair. More... | |
| int | mbedtls_rsa_check_pubkey (const mbedtls_rsa_context *ctx) |
| This function checks if a context contains at least an RSA public key. More... | |
| int | mbedtls_rsa_check_privkey (const mbedtls_rsa_context *ctx) |
| This function checks if a context contains an RSA private key and perform basic consistency checks. More... | |
| int | mbedtls_rsa_check_pub_priv (const mbedtls_rsa_context *pub, const mbedtls_rsa_context *prv) |
| This function checks a public-private RSA key pair. More... | |
| int | mbedtls_rsa_public (mbedtls_rsa_context *ctx, const unsigned char *input, unsigned char *output) |
| This function performs an RSA public key operation. More... | |
| int | mbedtls_rsa_private (mbedtls_rsa_context *ctx, int(*f_rng)(void *, unsigned char *, size_t), void *p_rng, const unsigned char *input, unsigned char *output) |
| This function performs an RSA private key operation. More... | |
| int | mbedtls_rsa_pkcs1_encrypt (mbedtls_rsa_context *ctx, int(*f_rng)(void *, unsigned char *, size_t), void *p_rng, size_t ilen, const unsigned char *input, unsigned char *output) |
| This function adds the message padding, then performs an RSA operation. More... | |
| int | mbedtls_rsa_rsaes_pkcs1_v15_encrypt (mbedtls_rsa_context *ctx, int(*f_rng)(void *, unsigned char *, size_t), void *p_rng, size_t ilen, const unsigned char *input, unsigned char *output) |
| This function performs a PKCS#1 v1.5 encryption operation (RSAES-PKCS1-v1_5-ENCRYPT). More... | |
| int | mbedtls_rsa_rsaes_oaep_encrypt (mbedtls_rsa_context *ctx, int(*f_rng)(void *, unsigned char *, size_t), void *p_rng, const unsigned char *label, size_t label_len, size_t ilen, const unsigned char *input, unsigned char *output) |
| This function performs a PKCS#1 v2.1 OAEP encryption operation (RSAES-OAEP-ENCRYPT). More... | |
| int | mbedtls_rsa_pkcs1_decrypt (mbedtls_rsa_context *ctx, int(*f_rng)(void *, unsigned char *, size_t), void *p_rng, size_t *olen, const unsigned char *input, unsigned char *output, size_t output_max_len) |
| This function performs an RSA operation, then removes the message padding. More... | |
| int | mbedtls_rsa_rsaes_pkcs1_v15_decrypt (mbedtls_rsa_context *ctx, int(*f_rng)(void *, unsigned char *, size_t), void *p_rng, size_t *olen, const unsigned char *input, unsigned char *output, size_t output_max_len) |
| This function performs a PKCS#1 v1.5 decryption operation (RSAES-PKCS1-v1_5-DECRYPT). More... | |
| int | mbedtls_rsa_rsaes_oaep_decrypt (mbedtls_rsa_context *ctx, int(*f_rng)(void *, unsigned char *, size_t), void *p_rng, const unsigned char *label, size_t label_len, size_t *olen, const unsigned char *input, unsigned char *output, size_t output_max_len) |
| This function performs a PKCS#1 v2.1 OAEP decryption operation (RSAES-OAEP-DECRYPT). More... | |
| int | mbedtls_rsa_pkcs1_sign (mbedtls_rsa_context *ctx, int(*f_rng)(void *, unsigned char *, size_t), void *p_rng, mbedtls_md_type_t md_alg, unsigned int hashlen, const unsigned char *hash, unsigned char *sig) |
| This function performs a private RSA operation to sign a message digest using PKCS#1. More... | |
| int | mbedtls_rsa_rsassa_pkcs1_v15_sign (mbedtls_rsa_context *ctx, int(*f_rng)(void *, unsigned char *, size_t), void *p_rng, mbedtls_md_type_t md_alg, unsigned int hashlen, const unsigned char *hash, unsigned char *sig) |
| This function performs a PKCS#1 v1.5 signature operation (RSASSA-PKCS1-v1_5-SIGN). More... | |
| int | mbedtls_rsa_rsassa_pss_sign_ext (mbedtls_rsa_context *ctx, int(*f_rng)(void *, unsigned char *, size_t), void *p_rng, mbedtls_md_type_t md_alg, unsigned int hashlen, const unsigned char *hash, int saltlen, unsigned char *sig) |
| This function performs a PKCS#1 v2.1 PSS signature operation (RSASSA-PSS-SIGN). More... | |
| int | mbedtls_rsa_rsassa_pss_sign (mbedtls_rsa_context *ctx, int(*f_rng)(void *, unsigned char *, size_t), void *p_rng, mbedtls_md_type_t md_alg, unsigned int hashlen, const unsigned char *hash, unsigned char *sig) |
| This function performs a PKCS#1 v2.1 PSS signature operation (RSASSA-PSS-SIGN). More... | |
| int | mbedtls_rsa_pkcs1_verify (mbedtls_rsa_context *ctx, mbedtls_md_type_t md_alg, unsigned int hashlen, const unsigned char *hash, const unsigned char *sig) |
| This function performs a public RSA operation and checks the message digest. More... | |
| int | mbedtls_rsa_rsassa_pkcs1_v15_verify (mbedtls_rsa_context *ctx, mbedtls_md_type_t md_alg, unsigned int hashlen, const unsigned char *hash, const unsigned char *sig) |
| This function performs a PKCS#1 v1.5 verification operation (RSASSA-PKCS1-v1_5-VERIFY). More... | |
| int | mbedtls_rsa_rsassa_pss_verify (mbedtls_rsa_context *ctx, mbedtls_md_type_t md_alg, unsigned int hashlen, const unsigned char *hash, const unsigned char *sig) |
| This function performs a PKCS#1 v2.1 PSS verification operation (RSASSA-PSS-VERIFY). More... | |
| int | mbedtls_rsa_rsassa_pss_verify_ext (mbedtls_rsa_context *ctx, mbedtls_md_type_t md_alg, unsigned int hashlen, const unsigned char *hash, mbedtls_md_type_t mgf1_hash_id, int expected_salt_len, const unsigned char *sig) |
| This function performs a PKCS#1 v2.1 PSS verification operation (RSASSA-PSS-VERIFY). More... | |
| int | mbedtls_rsa_copy (mbedtls_rsa_context *dst, const mbedtls_rsa_context *src) |
| This function copies the components of an RSA context. More... | |
| void | mbedtls_rsa_free (mbedtls_rsa_context *ctx) |
| This function frees the components of an RSA key. More... | |
| int | mbedtls_rsa_self_test (int verbose) |
| The RSA checkup routine. More... | |
Detailed Description
This file provides an API for the RSA public-key cryptosystem.
The RSA public-key cryptosystem is defined in Public-Key Cryptography Standards (PKCS) #1 v1.5: RSA Encryption and Public-Key Cryptography Standards (PKCS) #1 v2.1: RSA Cryptography Specifications.
Definition in file rsa.h.
Macro Definition Documentation
| #define MBEDTLS_ERR_RSA_BAD_INPUT_DATA -0x4080 |
| #define MBEDTLS_ERR_RSA_INVALID_PADDING -0x4100 |
| #define MBEDTLS_ERR_RSA_KEY_CHECK_FAILED -0x4200 |
| #define MBEDTLS_ERR_RSA_KEY_GEN_FAILED -0x4180 |
| #define MBEDTLS_ERR_RSA_OUTPUT_TOO_LARGE -0x4400 |
| #define MBEDTLS_ERR_RSA_PRIVATE_FAILED -0x4300 |
| #define MBEDTLS_ERR_RSA_PUBLIC_FAILED -0x4280 |
| #define MBEDTLS_ERR_RSA_RNG_FAILED -0x4480 |
| #define MBEDTLS_ERR_RSA_VERIFY_FAILED -0x4380 |
| #define MBEDTLS_RSA_CRYPT 2 |
| #define MBEDTLS_RSA_SIGN 1 |
Function Documentation
| int mbedtls_rsa_check_privkey | ( | const mbedtls_rsa_context * | ctx | ) |
This function checks if a context contains an RSA private key and perform basic consistency checks.
- Note
- The consistency checks performed by this function not only ensure that mbedtls_rsa_private() can be called successfully on the given context, but that the various parameters are mutually consistent with high probability, in the sense that mbedtls_rsa_public() and mbedtls_rsa_private() are inverses.
- Warning
- This function should catch accidental misconfigurations like swapping of parameters, but it cannot establish full trust in neither the quality nor the consistency of the key material that was used to setup the given RSA context:
- Consistency: Imported parameters that are irrelevant for the implementation might be silently dropped. If dropped, the current function does not have access to them, and therefore cannot check them. See mbedtls_rsa_complete(). If you want to check the consistency of the entire content of an PKCS1-encoded RSA private key, for example, you should use mbedtls_rsa_validate_params() before setting up the RSA context. Additionally, if the implementation performs empirical checks, these checks substantiate but do not guarantee consistency.
- Quality: This function is not expected to perform extended quality assessments like checking that the prime factors are safe. Additionally, it is the responsibility of the user to ensure the trustworthiness of the source of his RSA parameters, which goes beyond what is effectively checkable by the library.
- Parameters
-
ctx The initialized RSA context to check.
- Returns
0on success.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_check_pub_priv | ( | const mbedtls_rsa_context * | pub, |
| const mbedtls_rsa_context * | prv | ||
| ) |
This function checks a public-private RSA key pair.
It checks each of the contexts, and makes sure they match.
- Parameters
-
pub The initialized RSA context holding the public key. prv The initialized RSA context holding the private key.
- Returns
0on success.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_check_pubkey | ( | const mbedtls_rsa_context * | ctx | ) |
This function checks if a context contains at least an RSA public key.
If the function runs successfully, it is guaranteed that enough information is present to perform an RSA public key operation using mbedtls_rsa_public().
- Parameters
-
ctx The initialized RSA context to check.
- Returns
0on success.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_complete | ( | mbedtls_rsa_context * | ctx | ) |
This function completes an RSA context from a set of imported core parameters.
To setup an RSA public key, precisely N and E must have been imported.
To setup an RSA private key, sufficient information must be present for the other parameters to be derivable.
The default implementation supports the following:
-
Derive
P,QfromN,D,E. -
Derive
N,DfromP,Q,E.
Alternative implementations need not support these.
If this function runs successfully, it guarantees that the RSA context can be used for RSA operations without the risk of failure or crash.
- Warning
- This function need not perform consistency checks for the imported parameters. In particular, parameters that are not needed by the implementation might be silently discarded and left unchecked. To check the consistency of the key material, see mbedtls_rsa_check_privkey().
- Parameters
-
ctx The initialized RSA context holding imported parameters.
- Returns
0on success.- MBEDTLS_ERR_RSA_BAD_INPUT_DATA if the attempted derivations failed.
| int mbedtls_rsa_copy | ( | mbedtls_rsa_context * | dst, |
| const mbedtls_rsa_context * | src | ||
| ) |
This function copies the components of an RSA context.
- Parameters
-
dst The destination context. This must be initialized. src The source context. This must be initialized.
- Returns
0on success.- MBEDTLS_ERR_MPI_ALLOC_FAILED on memory allocation failure.
| int mbedtls_rsa_export | ( | const mbedtls_rsa_context * | ctx, |
| mbedtls_mpi * | N, | ||
| mbedtls_mpi * | P, | ||
| mbedtls_mpi * | Q, | ||
| mbedtls_mpi * | D, | ||
| mbedtls_mpi * | E | ||
| ) |
This function exports the core parameters of an RSA key.
If this function runs successfully, the non-NULL buffers pointed to by N, P, Q, D, and E are fully written, with additional unused space filled leading by zero Bytes.
Possible reasons for returning MBEDTLS_ERR_PLATFORM_FEATURE_UNSUPPORTED:
- An alternative RSA implementation is in use, which stores the key externally, and either cannot or should not export it into RAM.
-
A SW or HW implementation might not support a certain deduction. For example,
P,QfromN,D, andEif the former are not part of the implementation.
If the function fails due to an unsupported operation, the RSA context stays intact and remains usable.
- Parameters
-
ctx The initialized RSA context. N The MPI to hold the RSA modulus. This may be NULLif this field need not be exported.P The MPI to hold the first prime factor of N. This may beNULLif this field need not be exported.Q The MPI to hold the second prime factor of N. This may beNULLif this field need not be exported.D The MPI to hold the private exponent. This may be NULLif this field need not be exported.E The MPI to hold the public exponent. This may be NULLif this field need not be exported.
- Returns
0on success.- MBEDTLS_ERR_PLATFORM_FEATURE_UNSUPPORTED if exporting the requested parameters cannot be done due to missing functionality or because of security policies.
- A non-zero return code on any other failure.
| int mbedtls_rsa_export_crt | ( | const mbedtls_rsa_context * | ctx, |
| mbedtls_mpi * | DP, | ||
| mbedtls_mpi * | DQ, | ||
| mbedtls_mpi * | QP | ||
| ) |
This function exports CRT parameters of a private RSA key.
- Note
- Alternative RSA implementations not using CRT-parameters internally can implement this function based on mbedtls_rsa_deduce_opt().
- Parameters
-
ctx The initialized RSA context. DP The MPI to hold DmoduloP-1, orNULLif it need not be exported.DQ The MPI to hold DmoduloQ-1, orNULLif it need not be exported.QP The MPI to hold modular inverse of QmoduloP, orNULLif it need not be exported.
- Returns
0on success.- A non-zero error code on failure.
| int mbedtls_rsa_export_raw | ( | const mbedtls_rsa_context * | ctx, |
| unsigned char * | N, | ||
| size_t | N_len, | ||
| unsigned char * | P, | ||
| size_t | P_len, | ||
| unsigned char * | Q, | ||
| size_t | Q_len, | ||
| unsigned char * | D, | ||
| size_t | D_len, | ||
| unsigned char * | E, | ||
| size_t | E_len | ||
| ) |
This function exports core parameters of an RSA key in raw big-endian binary format.
If this function runs successfully, the non-NULL buffers pointed to by N, P, Q, D, and E are fully written, with additional unused space filled leading by zero Bytes.
Possible reasons for returning MBEDTLS_ERR_PLATFORM_FEATURE_UNSUPPORTED:
- An alternative RSA implementation is in use, which stores the key externally, and either cannot or should not export it into RAM.
-
A SW or HW implementation might not support a certain deduction. For example,
P,QfromN,D, andEif the former are not part of the implementation.
If the function fails due to an unsupported operation, the RSA context stays intact and remains usable.
- Note
- The length parameters are ignored if the corresponding buffer pointers are NULL.
- Parameters
-
ctx The initialized RSA context. N The Byte array to store the RSA modulus, or NULLif this field need not be exported.N_len The size of the buffer for the modulus. P The Byte array to hold the first prime factor of N, orNULLif this field need not be exported.P_len The size of the buffer for the first prime factor. Q The Byte array to hold the second prime factor of N, orNULLif this field need not be exported.Q_len The size of the buffer for the second prime factor. D The Byte array to hold the private exponent, or NULLif this field need not be exported.D_len The size of the buffer for the private exponent. E The Byte array to hold the public exponent, or NULLif this field need not be exported.E_len The size of the buffer for the public exponent.
- Returns
0on success.- MBEDTLS_ERR_PLATFORM_FEATURE_UNSUPPORTED if exporting the requested parameters cannot be done due to missing functionality or because of security policies.
- A non-zero return code on any other failure.
| void mbedtls_rsa_free | ( | mbedtls_rsa_context * | ctx | ) |
This function frees the components of an RSA key.
- Parameters
-
ctx The RSA context to free. May be NULL, in which case this function is a no-op. If it is notNULL, it must point to an initialized RSA context.
| int mbedtls_rsa_gen_key | ( | mbedtls_rsa_context * | ctx, |
| int(*)(void *, unsigned char *, size_t) | f_rng, | ||
| void * | p_rng, | ||
| unsigned int | nbits, | ||
| int | exponent | ||
| ) |
This function generates an RSA keypair.
- Note
- mbedtls_rsa_init() must be called before this function, to set up the RSA context.
- Parameters
-
ctx The initialized RSA context used to hold the key. f_rng The RNG function to be used for key generation. This is mandatory and must not be NULL.p_rng The RNG context to be passed to f_rng. This may beNULLiff_rngdoesn't need a context.nbits The size of the public key in bits. exponent The public exponent to use. For example, 65537. This must be odd and greater than1.
- Returns
0on success.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| size_t mbedtls_rsa_get_len | ( | const mbedtls_rsa_context * | ctx | ) |
This function retrieves the length of RSA modulus in Bytes.
- Parameters
-
ctx The initialized RSA context.
- Returns
- The length of the RSA modulus in Bytes.
| int mbedtls_rsa_import | ( | mbedtls_rsa_context * | ctx, |
| const mbedtls_mpi * | N, | ||
| const mbedtls_mpi * | P, | ||
| const mbedtls_mpi * | Q, | ||
| const mbedtls_mpi * | D, | ||
| const mbedtls_mpi * | E | ||
| ) |
This function imports a set of core parameters into an RSA context.
- Note
- This function can be called multiple times for successive imports, if the parameters are not simultaneously present.
Any sequence of calls to this function should be followed by a call to mbedtls_rsa_complete(), which checks and completes the provided information to a ready-for-use public or private RSA key.
- Note
- See mbedtls_rsa_complete() for more information on which parameters are necessary to set up a private or public RSA key.
- The imported parameters are copied and need not be preserved for the lifetime of the RSA context being set up.
- Parameters
-
ctx The initialized RSA context to store the parameters in. N The RSA modulus. This may be NULL.P The first prime factor of N. This may beNULL.Q The second prime factor of N. This may beNULL.D The private exponent. This may be NULL.E The public exponent. This may be NULL.
- Returns
0on success.- A non-zero error code on failure.
| int mbedtls_rsa_import_raw | ( | mbedtls_rsa_context * | ctx, |
| unsigned char const * | N, | ||
| size_t | N_len, | ||
| unsigned char const * | P, | ||
| size_t | P_len, | ||
| unsigned char const * | Q, | ||
| size_t | Q_len, | ||
| unsigned char const * | D, | ||
| size_t | D_len, | ||
| unsigned char const * | E, | ||
| size_t | E_len | ||
| ) |
This function imports core RSA parameters, in raw big-endian binary format, into an RSA context.
- Note
- This function can be called multiple times for successive imports, if the parameters are not simultaneously present.
Any sequence of calls to this function should be followed by a call to mbedtls_rsa_complete(), which checks and completes the provided information to a ready-for-use public or private RSA key.
- Note
- See mbedtls_rsa_complete() for more information on which parameters are necessary to set up a private or public RSA key.
- The imported parameters are copied and need not be preserved for the lifetime of the RSA context being set up.
- Parameters
-
ctx The initialized RSA context to store the parameters in. N The RSA modulus. This may be NULL.N_len The Byte length of N; it is ignored ifN== NULL.P The first prime factor of N. This may beNULL.P_len The Byte length of P; it ns ignored ifP== NULL.Q The second prime factor of N. This may beNULL.Q_len The Byte length of Q; it is ignored ifQ== NULL.D The private exponent. This may be NULL.D_len The Byte length of D; it is ignored ifD== NULL.E The public exponent. This may be NULL.E_len The Byte length of E; it is ignored ifE== NULL.
- Returns
0on success.- A non-zero error code on failure.
| void mbedtls_rsa_init | ( | mbedtls_rsa_context * | ctx | ) |
This function initializes an RSA context.
- Note
- This function initializes the padding and the hash identifier to respectively MBEDTLS_RSA_PKCS_V15 and MBEDTLS_MD_NONE. See mbedtls_rsa_set_padding() for more information about those parameters.
- Parameters
-
ctx The RSA context to initialize. This must not be NULL.
| int mbedtls_rsa_pkcs1_decrypt | ( | mbedtls_rsa_context * | ctx, |
| int(*)(void *, unsigned char *, size_t) | f_rng, | ||
| void * | p_rng, | ||
| size_t * | olen, | ||
| const unsigned char * | input, | ||
| unsigned char * | output, | ||
| size_t | output_max_len | ||
| ) |
This function performs an RSA operation, then removes the message padding.
It is the generic wrapper for performing a PKCS#1 decryption operation.
- Note
- The output buffer length
output_max_lenshould be as large as the sizectx->lenofctx->N(for example, 128 Bytes if RSA-1024 is used) to be able to hold an arbitrary decrypted message. If it is not large enough to hold the decryption of the particular ciphertext provided, the function returnsMBEDTLS_ERR_RSA_OUTPUT_TOO_LARGE.
- Parameters
-
ctx The initialized RSA context to use. f_rng The RNG function. This is used for blinding and is mandatory; see mbedtls_rsa_private() for more. p_rng The RNG context to be passed to f_rng. This may beNULLiff_rngdoesn't need a context.olen The address at which to store the length of the plaintext. This must not be NULL.input The ciphertext buffer. This must be a readable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.output The buffer used to hold the plaintext. This must be a writable buffer of length output_max_lenBytes.output_max_len The length in Bytes of the output buffer output.
- Returns
0on success.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_pkcs1_encrypt | ( | mbedtls_rsa_context * | ctx, |
| int(*)(void *, unsigned char *, size_t) | f_rng, | ||
| void * | p_rng, | ||
| size_t | ilen, | ||
| const unsigned char * | input, | ||
| unsigned char * | output | ||
| ) |
This function adds the message padding, then performs an RSA operation.
It is the generic wrapper for performing a PKCS#1 encryption operation.
- Parameters
-
ctx The initialized RSA context to use. f_rng The RNG to use. It is used for padding generation and it is mandatory. p_rng The RNG context to be passed to f_rng. May beNULLiff_rngdoesn't need a context argument.ilen The length of the plaintext in Bytes. input The input data to encrypt. This must be a readable buffer of size ilenBytes. It may beNULLifilen == 0.output The output buffer. This must be a writable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.
- Returns
0on success.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_pkcs1_sign | ( | mbedtls_rsa_context * | ctx, |
| int(*)(void *, unsigned char *, size_t) | f_rng, | ||
| void * | p_rng, | ||
| mbedtls_md_type_t | md_alg, | ||
| unsigned int | hashlen, | ||
| const unsigned char * | hash, | ||
| unsigned char * | sig | ||
| ) |
This function performs a private RSA operation to sign a message digest using PKCS#1.
It is the generic wrapper for performing a PKCS#1 signature.
- Note
- The
sigbuffer must be as large as the size ofctx->N. For example, 128 Bytes if RSA-1024 is used. -
For PKCS#1 v2.1 encoding, see comments on mbedtls_rsa_rsassa_pss_sign() for details on
md_algandhash_id.
- Parameters
-
ctx The initialized RSA context to use. f_rng The RNG function to use. This is mandatory and must not be NULL.p_rng The RNG context to be passed to f_rng. This may beNULLiff_rngdoesn't need a context argument.md_alg The message-digest algorithm used to hash the original data. Use MBEDTLS_MD_NONE for signing raw data. hashlen The length of the message digest or raw data in Bytes. If md_algis not MBEDTLS_MD_NONE, this must match the output length of the corresponding hash algorithm.hash The buffer holding the message digest or raw data. This must be a readable buffer of at least hashlenBytes.sig The buffer to hold the signature. This must be a writable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus. A buffer length of MBEDTLS_MPI_MAX_SIZE is always safe.
- Returns
0if the signing operation was successful.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_pkcs1_verify | ( | mbedtls_rsa_context * | ctx, |
| mbedtls_md_type_t | md_alg, | ||
| unsigned int | hashlen, | ||
| const unsigned char * | hash, | ||
| const unsigned char * | sig | ||
| ) |
This function performs a public RSA operation and checks the message digest.
This is the generic wrapper for performing a PKCS#1 verification.
- Note
- For PKCS#1 v2.1 encoding, see comments on mbedtls_rsa_rsassa_pss_verify() about
md_algandhash_id.
- Parameters
-
ctx The initialized RSA public key context to use. md_alg The message-digest algorithm used to hash the original data. Use MBEDTLS_MD_NONE for signing raw data. hashlen The length of the message digest or raw data in Bytes. If md_algis not MBEDTLS_MD_NONE, this must match the output length of the corresponding hash algorithm.hash The buffer holding the message digest or raw data. This must be a readable buffer of at least hashlenBytes.sig The buffer holding the signature. This must be a readable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.
- Returns
0if the verify operation was successful.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_private | ( | mbedtls_rsa_context * | ctx, |
| int(*)(void *, unsigned char *, size_t) | f_rng, | ||
| void * | p_rng, | ||
| const unsigned char * | input, | ||
| unsigned char * | output | ||
| ) |
This function performs an RSA private key operation.
- Note
- Blinding is used if and only if a PRNG is provided.
- If blinding is used, both the base of exponentation and the exponent are blinded, providing protection against some side-channel attacks.
- Warning
- It is deprecated and a security risk to not provide a PRNG here and thereby prevent the use of blinding. Future versions of the library may enforce the presence of a PRNG.
- Parameters
-
ctx The initialized RSA context to use. f_rng The RNG function, used for blinding. It is mandatory. p_rng The RNG context to pass to f_rng. This may beNULLiff_rngdoesn't need a context.input The input buffer. This must be a readable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.output The output buffer. This must be a writable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.
- Returns
0on success.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_public | ( | mbedtls_rsa_context * | ctx, |
| const unsigned char * | input, | ||
| unsigned char * | output | ||
| ) |
This function performs an RSA public key operation.
- Parameters
-
ctx The initialized RSA context to use. input The input buffer. This must be a readable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.output The output buffer. This must be a writable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.
- Note
- This function does not handle message padding.
-
Make sure to set
input[0] = 0 or ensure that input is smaller thanN.
- Returns
0on success.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_rsaes_oaep_decrypt | ( | mbedtls_rsa_context * | ctx, |
| int(*)(void *, unsigned char *, size_t) | f_rng, | ||
| void * | p_rng, | ||
| const unsigned char * | label, | ||
| size_t | label_len, | ||
| size_t * | olen, | ||
| const unsigned char * | input, | ||
| unsigned char * | output, | ||
| size_t | output_max_len | ||
| ) |
This function performs a PKCS#1 v2.1 OAEP decryption operation (RSAES-OAEP-DECRYPT).
- Note
- The output buffer length
output_max_lenshould be as large as the sizectx->lenofctx->N, for example, 128 Bytes if RSA-1024 is used, to be able to hold an arbitrary decrypted message. If it is not large enough to hold the decryption of the particular ciphertext provided, the function returns MBEDTLS_ERR_RSA_OUTPUT_TOO_LARGE.
- Parameters
-
ctx The initialized RSA context to use. f_rng The RNG function. This is used for blinding and is mandatory. p_rng The RNG context to be passed to f_rng. This may beNULLiff_rngdoesn't need a context.label The buffer holding the custom label to use. This must be a readable buffer of length label_lenBytes. It may beNULLiflabel_lenis0.label_len The length of the label in Bytes. olen The address at which to store the length of the plaintext. This must not be NULL.input The ciphertext buffer. This must be a readable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.output The buffer used to hold the plaintext. This must be a writable buffer of length output_max_lenBytes.output_max_len The length in Bytes of the output buffer output.
- Returns
0on success.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_rsaes_oaep_encrypt | ( | mbedtls_rsa_context * | ctx, |
| int(*)(void *, unsigned char *, size_t) | f_rng, | ||
| void * | p_rng, | ||
| const unsigned char * | label, | ||
| size_t | label_len, | ||
| size_t | ilen, | ||
| const unsigned char * | input, | ||
| unsigned char * | output | ||
| ) |
This function performs a PKCS#1 v2.1 OAEP encryption operation (RSAES-OAEP-ENCRYPT).
- Note
- The output buffer must be as large as the size of ctx->N. For example, 128 Bytes if RSA-1024 is used.
- Parameters
-
ctx The initnialized RSA context to use. f_rng The RNG function to use. This is needed for padding generation and is mandatory. p_rng The RNG context to be passed to f_rng. This may beNULLiff_rngdoesn't need a context argument.label The buffer holding the custom label to use. This must be a readable buffer of length label_lenBytes. It may beNULLiflabel_lenis0.label_len The length of the label in Bytes. ilen The length of the plaintext buffer inputin Bytes.input The input data to encrypt. This must be a readable buffer of size ilenBytes. It may beNULLifilen == 0.output The output buffer. This must be a writable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.
- Returns
0on success.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_rsaes_pkcs1_v15_decrypt | ( | mbedtls_rsa_context * | ctx, |
| int(*)(void *, unsigned char *, size_t) | f_rng, | ||
| void * | p_rng, | ||
| size_t * | olen, | ||
| const unsigned char * | input, | ||
| unsigned char * | output, | ||
| size_t | output_max_len | ||
| ) |
This function performs a PKCS#1 v1.5 decryption operation (RSAES-PKCS1-v1_5-DECRYPT).
- Note
- The output buffer length
output_max_lenshould be as large as the sizectx->lenofctx->N, for example, 128 Bytes if RSA-1024 is used, to be able to hold an arbitrary decrypted message. If it is not large enough to hold the decryption of the particular ciphertext provided, the function returns MBEDTLS_ERR_RSA_OUTPUT_TOO_LARGE.
- Parameters
-
ctx The initialized RSA context to use. f_rng The RNG function. This is used for blinding and is mandatory; see mbedtls_rsa_private() for more. p_rng The RNG context to be passed to f_rng. This may beNULLiff_rngdoesn't need a context.olen The address at which to store the length of the plaintext. This must not be NULL.input The ciphertext buffer. This must be a readable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.output The buffer used to hold the plaintext. This must be a writable buffer of length output_max_lenBytes.output_max_len The length in Bytes of the output buffer output.
- Returns
0on success.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_rsaes_pkcs1_v15_encrypt | ( | mbedtls_rsa_context * | ctx, |
| int(*)(void *, unsigned char *, size_t) | f_rng, | ||
| void * | p_rng, | ||
| size_t | ilen, | ||
| const unsigned char * | input, | ||
| unsigned char * | output | ||
| ) |
This function performs a PKCS#1 v1.5 encryption operation (RSAES-PKCS1-v1_5-ENCRYPT).
- Parameters
-
ctx The initialized RSA context to use. f_rng The RNG function to use. It is mandatory and used for padding generation. p_rng The RNG context to be passed to f_rng. This may beNULLiff_rngdoesn't need a context argument.ilen The length of the plaintext in Bytes. input The input data to encrypt. This must be a readable buffer of size ilenBytes. It may beNULLifilen == 0.output The output buffer. This must be a writable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.
- Returns
0on success.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_rsassa_pkcs1_v15_sign | ( | mbedtls_rsa_context * | ctx, |
| int(*)(void *, unsigned char *, size_t) | f_rng, | ||
| void * | p_rng, | ||
| mbedtls_md_type_t | md_alg, | ||
| unsigned int | hashlen, | ||
| const unsigned char * | hash, | ||
| unsigned char * | sig | ||
| ) |
This function performs a PKCS#1 v1.5 signature operation (RSASSA-PKCS1-v1_5-SIGN).
- Parameters
-
ctx The initialized RSA context to use. f_rng The RNG function. This is used for blinding and is mandatory; see mbedtls_rsa_private() for more. p_rng The RNG context to be passed to f_rng. This may beNULLiff_rngdoesn't need a context argument.md_alg The message-digest algorithm used to hash the original data. Use MBEDTLS_MD_NONE for signing raw data. hashlen The length of the message digest or raw data in Bytes. If md_algis not MBEDTLS_MD_NONE, this must match the output length of the corresponding hash algorithm.hash The buffer holding the message digest or raw data. This must be a readable buffer of at least hashlenBytes.sig The buffer to hold the signature. This must be a writable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus. A buffer length of MBEDTLS_MPI_MAX_SIZE is always safe.
- Returns
0if the signing operation was successful.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_rsassa_pkcs1_v15_verify | ( | mbedtls_rsa_context * | ctx, |
| mbedtls_md_type_t | md_alg, | ||
| unsigned int | hashlen, | ||
| const unsigned char * | hash, | ||
| const unsigned char * | sig | ||
| ) |
This function performs a PKCS#1 v1.5 verification operation (RSASSA-PKCS1-v1_5-VERIFY).
- Parameters
-
ctx The initialized RSA public key context to use. md_alg The message-digest algorithm used to hash the original data. Use MBEDTLS_MD_NONE for signing raw data. hashlen The length of the message digest or raw data in Bytes. If md_algis not MBEDTLS_MD_NONE, this must match the output length of the corresponding hash algorithm.hash The buffer holding the message digest or raw data. This must be a readable buffer of at least hashlenBytes.sig The buffer holding the signature. This must be a readable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.
- Returns
0if the verify operation was successful.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_rsassa_pss_sign | ( | mbedtls_rsa_context * | ctx, |
| int(*)(void *, unsigned char *, size_t) | f_rng, | ||
| void * | p_rng, | ||
| mbedtls_md_type_t | md_alg, | ||
| unsigned int | hashlen, | ||
| const unsigned char * | hash, | ||
| unsigned char * | sig | ||
| ) |
This function performs a PKCS#1 v2.1 PSS signature operation (RSASSA-PSS-SIGN).
- Note
- The
hash_idset inctxby calling mbedtls_rsa_set_padding() selects the hash used for the encoding operation and for the mask generation function (MGF1). For more details on the encoding operation and the mask generation function, consult RFC-3447: Public-Key Cryptography Standards (PKCS) #1 v2.1: RSA Cryptography Specifications. - This function always uses the maximum possible salt size, up to the length of the payload hash. This choice of salt size complies with FIPS 186-4 §5.5 (e) and RFC 8017 (PKCS#1 v2.2) §9.1.1 step 3. Furthermore this function enforces a minimum salt size which is the hash size minus 2 bytes. If this minimum size is too large given the key size (the salt size, plus the hash size, plus 2 bytes must be no more than the key size in bytes), this function returns MBEDTLS_ERR_RSA_BAD_INPUT_DATA.
- Parameters
-
ctx The initialized RSA context to use. f_rng The RNG function. It is mandatory and must not be NULL.p_rng The RNG context to be passed to f_rng. This may beNULLiff_rngdoesn't need a context argument.md_alg The message-digest algorithm used to hash the original data. Use MBEDTLS_MD_NONE for signing raw data. hashlen The length of the message digest or raw data in Bytes. If md_algis not MBEDTLS_MD_NONE, this must match the output length of the corresponding hash algorithm.hash The buffer holding the message digest or raw data. This must be a readable buffer of at least hashlenBytes.sig The buffer to hold the signature. This must be a writable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus. A buffer length of MBEDTLS_MPI_MAX_SIZE is always safe.
- Returns
0if the signing operation was successful.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_rsassa_pss_sign_ext | ( | mbedtls_rsa_context * | ctx, |
| int(*)(void *, unsigned char *, size_t) | f_rng, | ||
| void * | p_rng, | ||
| mbedtls_md_type_t | md_alg, | ||
| unsigned int | hashlen, | ||
| const unsigned char * | hash, | ||
| int | saltlen, | ||
| unsigned char * | sig | ||
| ) |
This function performs a PKCS#1 v2.1 PSS signature operation (RSASSA-PSS-SIGN).
- Note
- The
hash_idset inctxby calling mbedtls_rsa_set_padding() selects the hash used for the encoding operation and for the mask generation function (MGF1). For more details on the encoding operation and the mask generation function, consult RFC-3447: Public-Key Cryptography Standards (PKCS) #1 v2.1: RSA Cryptography Specifications. - This function enforces that the provided salt length complies with FIPS 186-4 §5.5 (e) and RFC 8017 (PKCS#1 v2.2) §9.1.1 step 3. The constraint is that the hash length plus the salt length plus 2 bytes must be at most the key length. If this constraint is not met, this function returns MBEDTLS_ERR_RSA_BAD_INPUT_DATA.
- Parameters
-
ctx The initialized RSA context to use. f_rng The RNG function. It is mandatory and must not be NULL.p_rng The RNG context to be passed to f_rng. This may beNULLiff_rngdoesn't need a context argument.md_alg The message-digest algorithm used to hash the original data. Use MBEDTLS_MD_NONE for signing raw data. hashlen The length of the message digest or raw data in Bytes. If md_algis not MBEDTLS_MD_NONE, this must match the output length of the corresponding hash algorithm.hash The buffer holding the message digest or raw data. This must be a readable buffer of at least hashlenBytes.saltlen The length of the salt that should be used. If passed MBEDTLS_RSA_SALT_LEN_ANY, the function will use the largest possible salt length up to the hash length, which is the largest permitted by some standards including FIPS 186-4 §5.5. sig The buffer to hold the signature. This must be a writable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus. A buffer length of MBEDTLS_MPI_MAX_SIZE is always safe.
- Returns
0if the signing operation was successful.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_rsassa_pss_verify | ( | mbedtls_rsa_context * | ctx, |
| mbedtls_md_type_t | md_alg, | ||
| unsigned int | hashlen, | ||
| const unsigned char * | hash, | ||
| const unsigned char * | sig | ||
| ) |
This function performs a PKCS#1 v2.1 PSS verification operation (RSASSA-PSS-VERIFY).
- Note
- The
hash_idset inctxby calling mbedtls_rsa_set_padding() selects the hash used for the encoding operation and for the mask generation function (MGF1). For more details on the encoding operation and the mask generation function, consult RFC-3447: Public-Key Cryptography Standards (PKCS) #1 v2.1: RSA Cryptography Specifications. If thehash_idset inctxby mbedtls_rsa_set_padding() is MBEDTLS_MD_NONE, themd_algparameter is used.
- Parameters
-
ctx The initialized RSA public key context to use. md_alg The message-digest algorithm used to hash the original data. Use MBEDTLS_MD_NONE for signing raw data. hashlen The length of the message digest or raw data in Bytes. If md_algis not MBEDTLS_MD_NONE, this must match the output length of the corresponding hash algorithm.hash The buffer holding the message digest or raw data. This must be a readable buffer of at least hashlenBytes.sig The buffer holding the signature. This must be a readable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.
- Returns
0if the verify operation was successful.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_rsassa_pss_verify_ext | ( | mbedtls_rsa_context * | ctx, |
| mbedtls_md_type_t | md_alg, | ||
| unsigned int | hashlen, | ||
| const unsigned char * | hash, | ||
| mbedtls_md_type_t | mgf1_hash_id, | ||
| int | expected_salt_len, | ||
| const unsigned char * | sig | ||
| ) |
This function performs a PKCS#1 v2.1 PSS verification operation (RSASSA-PSS-VERIFY).
- Note
- The
sigbuffer must be as large as the size ofctx->N. For example, 128 Bytes if RSA-1024 is used. -
The
hash_idset inctxby mbedtls_rsa_set_padding() is ignored.
- Parameters
-
ctx The initialized RSA public key context to use. md_alg The message-digest algorithm used to hash the original data. Use MBEDTLS_MD_NONE for signing raw data. hashlen The length of the message digest or raw data in Bytes. If md_algis not MBEDTLS_MD_NONE, this must match the output length of the corresponding hash algorithm.hash The buffer holding the message digest or raw data. This must be a readable buffer of at least hashlenBytes.mgf1_hash_id The message digest algorithm used for the verification operation and the mask generation function (MGF1). For more details on the encoding operation and the mask generation function, consult RFC-3447: Public-Key Cryptography Standards (PKCS) #1 v2.1: RSA Cryptography Specifications. expected_salt_len The length of the salt used in padding. Use MBEDTLS_RSA_SALT_LEN_ANY to accept any salt length. sig The buffer holding the signature. This must be a readable buffer of length ctx->lenBytes. For example,256Bytes for an 2048-bit RSA modulus.
- Returns
0if the verify operation was successful.-
An
MBEDTLS_ERR_RSA_XXXerror code on failure.
| int mbedtls_rsa_self_test | ( | int | verbose | ) |
The RSA checkup routine.
- Returns
0on success.-
1on failure.
| int mbedtls_rsa_set_padding | ( | mbedtls_rsa_context * | ctx, |
| int | padding, | ||
| mbedtls_md_type_t | hash_id | ||
| ) |
This function sets padding for an already initialized RSA context.
- Note
- Set padding to MBEDTLS_RSA_PKCS_V21 for the RSAES-OAEP encryption scheme and the RSASSA-PSS signature scheme.
-
The
hash_idparameter is ignored when using MBEDTLS_RSA_PKCS_V15 padding. -
The choice of padding mode is strictly enforced for private key operations, since there might be security concerns in mixing padding modes. For public key operations it is a default value, which can be overridden by calling specific
mbedtls_rsa_rsaes_xxxormbedtls_rsa_rsassa_xxxfunctions. -
The hash selected in
hash_idis always used for OEAP encryption. For PSS signatures, it is always used for making signatures, but can be overridden for verifying them. If set to MBEDTLS_MD_NONE, it is always overridden.
- Parameters
-
ctx The initialized RSA context to be configured. padding The padding mode to use. This must be either MBEDTLS_RSA_PKCS_V15 or MBEDTLS_RSA_PKCS_V21. hash_id The hash identifier for PSS or OAEP, if paddingis MBEDTLS_RSA_PKCS_V21. MBEDTLS_MD_NONE is accepted by this function but may be not suitable for some operations. Ignored ifpaddingis MBEDTLS_RSA_PKCS_V15.
- Returns
0on success.-
MBEDTLS_ERR_RSA_INVALID_PADDING failure:
paddingorhash_idis invalid.
 1.8.6
1.8.6