|
Mbed TLS v4.0.0
|
|
Mbed TLS v4.0.0
|
Public Key abstraction layer. More...
#include "mbedtls/private_access.h"#include "tf-psa-crypto/build_info.h"#include "mbedtls/compat-3-crypto.h"#include "mbedtls/md.h"#include "psa/crypto.h"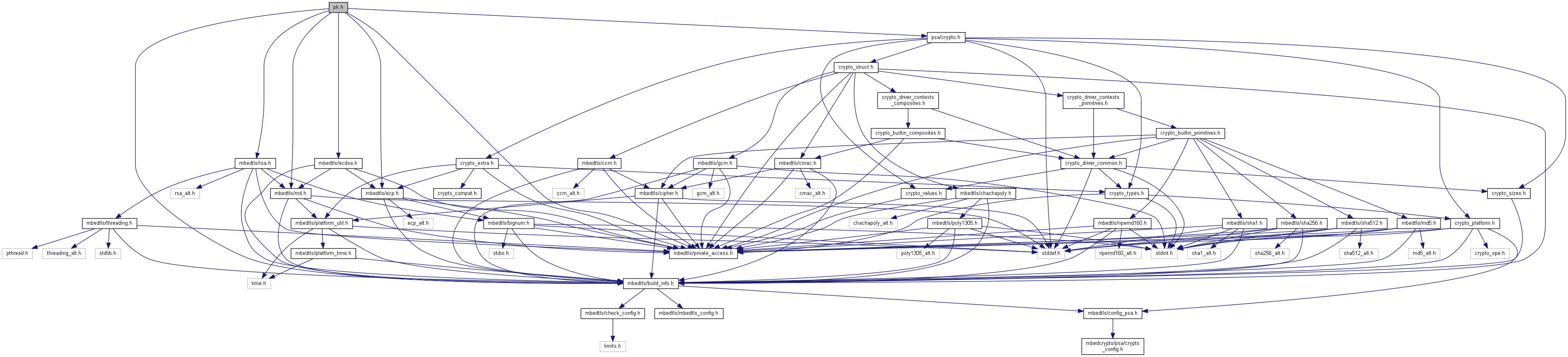
Go to the source code of this file.
Data Structures | |
| struct | mbedtls_pk_context |
| Public key container. More... | |
| struct | mbedtls_pk_restart_ctx |
| Context for resuming operations. More... | |
Typedefs | |
| typedef struct mbedtls_pk_info_t | mbedtls_pk_info_t |
| typedef struct mbedtls_pk_context | mbedtls_pk_context |
| Public key container. More... | |
Enumerations | |
| enum | mbedtls_pk_sigalg_t { MBEDTLS_PK_SIGALG_NONE = 0, MBEDTLS_PK_SIGALG_RSA_PKCS1V15, MBEDTLS_PK_SIGALG_RSA_PSS, MBEDTLS_PK_SIGALG_ECDSA } |
| enum | mbedtls_pk_rsa_padding_t { MBEDTLS_PK_RSA_PKCS_V15 = 0, MBEDTLS_PK_RSA_PKCS_V21 } |
Functions | |
| void | mbedtls_pk_init (mbedtls_pk_context *ctx) |
| Initialize a mbedtls_pk_context (as empty). More... | |
| void | mbedtls_pk_free (mbedtls_pk_context *ctx) |
| Empty a mbedtls_pk_context. After this, the context can be re-used as if it had been freshly initialized. More... | |
| void | mbedtls_pk_restart_init (mbedtls_pk_restart_ctx *ctx) |
| Initialize a restart context. More... | |
| void | mbedtls_pk_restart_free (mbedtls_pk_restart_ctx *ctx) |
| Free the components of a restart context. More... | |
| int | mbedtls_pk_wrap_psa (mbedtls_pk_context *ctx, const mbedtls_svc_key_id_t key) |
| Populate a PK context by wrapping a PSA key pair. More... | |
| size_t | mbedtls_pk_get_bitlen (const mbedtls_pk_context *ctx) |
| Get the size in bits of the underlying key. More... | |
| int | mbedtls_pk_can_do_psa (const mbedtls_pk_context *pk, psa_algorithm_t alg, psa_key_usage_t usage) |
Tell if the key wrapped in the PK context is able to perform the usage operation using the alg algorithm. More... | |
| int | mbedtls_pk_get_psa_attributes (const mbedtls_pk_context *pk, psa_key_usage_t usage, psa_key_attributes_t *attributes) |
| Determine valid PSA attributes that can be used to import a key into PSA. More... | |
| int | mbedtls_pk_import_into_psa (const mbedtls_pk_context *pk, const psa_key_attributes_t *attributes, mbedtls_svc_key_id_t *key_id) |
| Import a key into the PSA key store. More... | |
| int | mbedtls_pk_copy_from_psa (mbedtls_svc_key_id_t key_id, mbedtls_pk_context *pk) |
| Populate a PK context with the key material from a PSA key. More... | |
| int | mbedtls_pk_copy_public_from_psa (mbedtls_svc_key_id_t key_id, mbedtls_pk_context *pk) |
| Populate a PK context with the public key material of a PSA key. More... | |
| int | mbedtls_pk_verify (mbedtls_pk_context *ctx, mbedtls_md_type_t md_alg, const unsigned char *hash, size_t hash_len, const unsigned char *sig, size_t sig_len) |
| Verify signature. More... | |
| int | mbedtls_pk_verify_restartable (mbedtls_pk_context *ctx, mbedtls_md_type_t md_alg, const unsigned char *hash, size_t hash_len, const unsigned char *sig, size_t sig_len, mbedtls_pk_restart_ctx *rs_ctx) |
Restartable version of mbedtls_pk_verify() More... | |
| int | mbedtls_pk_verify_ext (mbedtls_pk_sigalg_t type, mbedtls_pk_context *ctx, mbedtls_md_type_t md_alg, const unsigned char *hash, size_t hash_len, const unsigned char *sig, size_t sig_len) |
| Verify signature, selecting a specific algorithm. More... | |
| int | mbedtls_pk_sign (mbedtls_pk_context *ctx, mbedtls_md_type_t md_alg, const unsigned char *hash, size_t hash_len, unsigned char *sig, size_t sig_size, size_t *sig_len) |
| Make signature. More... | |
| int | mbedtls_pk_sign_restartable (mbedtls_pk_context *ctx, mbedtls_md_type_t md_alg, const unsigned char *hash, size_t hash_len, unsigned char *sig, size_t sig_size, size_t *sig_len, mbedtls_pk_restart_ctx *rs_ctx) |
Restartable version of mbedtls_pk_sign() More... | |
| int | mbedtls_pk_sign_ext (mbedtls_pk_sigalg_t sig_type, mbedtls_pk_context *ctx, mbedtls_md_type_t md_alg, const unsigned char *hash, size_t hash_len, unsigned char *sig, size_t sig_size, size_t *sig_len) |
| Generate a signature, selecting a specific algorithm. More... | |
| int | mbedtls_pk_check_pair (const mbedtls_pk_context *pub, const mbedtls_pk_context *prv) |
| Check if a public-private pair of keys matches. More... | |
| int | mbedtls_pk_parse_key (mbedtls_pk_context *ctx, const unsigned char *key, size_t keylen, const unsigned char *pwd, size_t pwdlen) |
| Parse a private key in PEM or DER format. More... | |
| int | mbedtls_pk_parse_public_key (mbedtls_pk_context *ctx, const unsigned char *key, size_t keylen) |
| Parse a public key in PEM or DER format. More... | |
| int | mbedtls_pk_parse_keyfile (mbedtls_pk_context *ctx, const char *path, const char *password) |
| Load and parse a private key. More... | |
| int | mbedtls_pk_parse_public_keyfile (mbedtls_pk_context *ctx, const char *path) |
| Load and parse a public key. More... | |
| int | mbedtls_pk_write_key_der (const mbedtls_pk_context *ctx, unsigned char *buf, size_t size) |
| Write a private key to a PKCS#1 or SEC1 DER structure Note: data is written at the end of the buffer! Use the return value to determine where you should start using the buffer. More... | |
| int | mbedtls_pk_write_pubkey_der (const mbedtls_pk_context *ctx, unsigned char *buf, size_t size) |
| Write a public key to a SubjectPublicKeyInfo DER structure Note: data is written at the end of the buffer! Use the return value to determine where you should start using the buffer. More... | |
| int | mbedtls_pk_write_pubkey_pem (const mbedtls_pk_context *ctx, unsigned char *buf, size_t size) |
| Write a public key to a PEM string. More... | |
| int | mbedtls_pk_write_key_pem (const mbedtls_pk_context *ctx, unsigned char *buf, size_t size) |
| Write a private key to a PKCS#1 or SEC1 PEM string. More... | |
Public Key abstraction layer.
Definition in file pk.h.
| #define MBEDTLS_ERR_PK_FEATURE_UNAVAILABLE -0x3980 |
| #define MBEDTLS_ERR_PK_FILE_IO_ERROR -0x3E00 |
| #define MBEDTLS_ERR_PK_INVALID_ALG -0x3A80 |
| #define MBEDTLS_ERR_PK_INVALID_PUBKEY -0x3B00 |
| #define MBEDTLS_ERR_PK_KEY_INVALID_FORMAT -0x3D00 |
| #define MBEDTLS_ERR_PK_KEY_INVALID_VERSION -0x3D80 |
| #define MBEDTLS_ERR_PK_PASSWORD_MISMATCH -0x3B80 |
| #define MBEDTLS_ERR_PK_PASSWORD_REQUIRED -0x3C00 |
| #define MBEDTLS_ERR_PK_TYPE_MISMATCH -0x3F00 |
| #define MBEDTLS_ERR_PK_UNKNOWN_NAMED_CURVE -0x3A00 |
| #define MBEDTLS_ERR_PK_UNKNOWN_PK_ALG -0x3C80 |
| #define MBEDTLS_PK_ALG_ECDSA | ( | hash_alg | ) | PSA_ALG_DETERMINISTIC_ECDSA(hash_alg) |
| #define MBEDTLS_PK_MAX_EC_PUBKEY_RAW_LEN PSA_KEY_EXPORT_ECC_PUBLIC_KEY_MAX_SIZE(PSA_VENDOR_ECC_MAX_CURVE_BITS) |
| #define MBEDTLS_PK_MAX_PUBKEY_RAW_LEN |
| #define MBEDTLS_PK_MAX_RSA_PUBKEY_RAW_LEN PSA_KEY_EXPORT_RSA_PUBLIC_KEY_MAX_SIZE(PSA_VENDOR_RSA_MAX_KEY_BITS) |
| #define MBEDTLS_PK_SIGNATURE_MAX_SIZE 0 |
Maximum size of a signature made by mbedtls_pk_sign() and other signature functions.
| #define MBEDTLS_PK_SIGNATURE_MAX_SIZE MBEDTLS_MPI_MAX_SIZE |
Maximum size of a signature made by mbedtls_pk_sign() and other signature functions.
| typedef struct mbedtls_pk_context mbedtls_pk_context |
Public key container.
| typedef struct mbedtls_pk_info_t mbedtls_pk_info_t |
| enum mbedtls_pk_sigalg_t |
| int mbedtls_pk_can_do_psa | ( | const mbedtls_pk_context * | pk, |
| psa_algorithm_t | alg, | ||
| psa_key_usage_t | usage | ||
| ) |
Tell if the key wrapped in the PK context is able to perform the usage operation using the alg algorithm.
The operation may be a PK function, a PSA operation on the underlying PSA key if the PK object wraps a PSA key, or a PSA operation on a key obtained with mbedtls_pk_import_into_psa().
0 if the key type and policy are suitable for the requested algorithm and usage, even if the key would not work for some other reason, for example an RSA key that is too small for OAEP with the specified hash. This behavior may change without notice in future versions of the library.| pk | The context to query. It must have been populated. |
| alg | PSA algorithm to check against. Allowed values are:
|
| usage | PSA usage flag that the key must be verified against. A single flag from the following list must be specified: |
| int mbedtls_pk_check_pair | ( | const mbedtls_pk_context * | pub, |
| const mbedtls_pk_context * | prv | ||
| ) |
Check if a public-private pair of keys matches.
mbedtls_pk_wrap_psa().| pub | Context holding a public key. |
| prv | Context holding a private (and public) key. |
0 on success (keys were checked and match each other). | int mbedtls_pk_copy_from_psa | ( | mbedtls_svc_key_id_t | key_id, |
| mbedtls_pk_context * | pk | ||
| ) |
Populate a PK context with the key material from a PSA key.
This key:
Once this function returns the PK object will be completely independent from the original PSA key that it was generated from.
mbedtls_pk_get_psa_attributes() for details on which algorithm is going to be used by PK for contexts populated with this function.If you want to retain the PSA policy, see mbedtls_pk_wrap_psa() - but then the PSA key needs to live at least as long as the PK context.
| key_id | The key identifier of the key stored in PSA. |
| pk | The PK context to populate. It must be empty. |
| int mbedtls_pk_copy_public_from_psa | ( | mbedtls_svc_key_id_t | key_id, |
| mbedtls_pk_context * | pk | ||
| ) |
Populate a PK context with the public key material of a PSA key.
The key must be an RSA or ECC key. It can be either a public key or a key pair, and only the public key is copied.
Once this function returns the PK object will be completely independent from the original PSA key that it was generated from.
mbedtls_pk_get_psa_attributes() for details on which algorithm is going to be used by PK for contexts populated with this function.If you want to retain the PSA policy, see mbedtls_pk_wrap_psa() - but then the PSA key needs to live at least as long as the PK context.
| key_id | The key identifier of the key stored in PSA. |
| pk | The PK context to populate. It must be empty. |
| void mbedtls_pk_free | ( | mbedtls_pk_context * | ctx | ) |
Empty a mbedtls_pk_context. After this, the context can be re-used as if it had been freshly initialized.
| ctx | The context to clear. It must have been initialized. If this is NULL, this function does nothing. |
| size_t mbedtls_pk_get_bitlen | ( | const mbedtls_pk_context * | ctx | ) |
Get the size in bits of the underlying key.
| ctx | The context to query. It must have been populated. |
| int mbedtls_pk_get_psa_attributes | ( | const mbedtls_pk_context * | pk, |
| psa_key_usage_t | usage, | ||
| psa_key_attributes_t * | attributes | ||
| ) |
Determine valid PSA attributes that can be used to import a key into PSA.
The attributes determined by this function are suitable for calling mbedtls_pk_import_into_psa() to create a PSA key with the same key material.
The typical flow of operations involving this function is ``` psa_key_attributes_t attributes = PSA_KEY_ATTRIBUTES_INIT; int ret = mbedtls_pk_get_psa_attributes(pk, &attributes); if (ret != 0) ...; // error handling omitted // Tweak attributes if desired psa_key_id_t key_id = 0; ret = mbedtls_pk_import_into_psa(pk, &attributes, &key_id); if (ret != 0) ...; // error handling omitted ```
| [in] | pk | The PK context to use. It must have been populated. It can either contain a key pair or just a public key. |
| usage | A single PSA_KEY_USAGE_xxx flag among the following:
| |
| [out] | attributes | On success, valid attributes to import the key into PSA.
|
pk does not contain a key compatible with the desired usage. Another error code on other failures. | int mbedtls_pk_import_into_psa | ( | const mbedtls_pk_context * | pk, |
| const psa_key_attributes_t * | attributes, | ||
| mbedtls_svc_key_id_t * | key_id | ||
| ) |
Import a key into the PSA key store.
This function is equivalent to calling psa_import_key() with the key material from pk.
The typical way to use this function is:
psa_set_key_type(&attributes,
PSA_KEY_TYPE_PUBLIC_KEY_OF_KEY_PAIR(
psa_get_key_type(&attributes)));
| [in] | pk | The PK context to use. It must have been populated. It can either contain a key pair or just a public key. |
| [in] | attributes | The attributes to use for the new key. They must be compatible with pk. In particular, the key type must match the content of pk. If pk contains a key pair, the key type in attributes can be either the key pair type or the corresponding public key type (to import only the public part). |
| [out] | key_id | On success, the identifier of the newly created key. On error, this is MBEDTLS_SVC_KEY_ID_INIT. |
pk does not contain a key of the type identified in attributes. Another error code on other failures. | void mbedtls_pk_init | ( | mbedtls_pk_context * | ctx | ) |
Initialize a mbedtls_pk_context (as empty).
After this, you want to populate the context using one of the following functions:
mbedtls_pk_wrap_psa() mbedtls_pk_copy_from_psa() mbedtls_pk_copy_public_from_psa() mbedtls_pk_parse_key() mbedtls_pk_parse_public_key() mbedtls_pk_parse_keyfile() mbedtls_pk_parse_public_keyfile() | ctx | The context to initialize. This must not be NULL. |
| int mbedtls_pk_parse_key | ( | mbedtls_pk_context * | ctx, |
| const unsigned char * | key, | ||
| size_t | keylen, | ||
| const unsigned char * | pwd, | ||
| size_t | pwdlen | ||
| ) |
Parse a private key in PEM or DER format.
| ctx | The PK context to populate. It must be empty. |
| key | Input buffer to parse. The buffer must contain the input exactly, with no extra trailing material. For PEM, the buffer must contain a null-terminated string. |
| keylen | Size of key in bytes. For PEM data, this includes the terminating null byte, so keylen must be equal to strlen(key) + 1. |
| pwd | Optional password for decryption. Pass NULL if expecting a non-encrypted key. Pass a string of pwdlen bytes if expecting an encrypted key; a non-encrypted key will also be accepted. The empty password is not supported. |
| pwdlen | Size of the password in bytes. Ignored if pwd is NULL. |
mbedtls_pk_can_do_psa().| int mbedtls_pk_parse_keyfile | ( | mbedtls_pk_context * | ctx, |
| const char * | path, | ||
| const char * | password | ||
| ) |
Load and parse a private key.
| ctx | The PK context to populate. It must be empty. |
| path | filename to read the private key from |
| password | Optional password to decrypt the file. Pass NULL if expecting a non-encrypted key. Pass a null-terminated string if expecting an encrypted key; a non-encrypted key will also be accepted. The empty password is not supported. |
mbedtls_pk_can_do_psa().| int mbedtls_pk_parse_public_key | ( | mbedtls_pk_context * | ctx, |
| const unsigned char * | key, | ||
| size_t | keylen | ||
| ) |
Parse a public key in PEM or DER format.
| ctx | The PK context to populate. It must be empty. |
| key | Input buffer to parse. The buffer must contain the input exactly, with no extra trailing material. For PEM, the buffer must contain a null-terminated string. |
| keylen | Size of key in bytes. For PEM data, this includes the terminating null byte, so keylen must be equal to strlen(key) + 1. |
mbedtls_pk_can_do_psa().| int mbedtls_pk_parse_public_keyfile | ( | mbedtls_pk_context * | ctx, |
| const char * | path | ||
| ) |
Load and parse a public key.
| ctx | The PK context to populate. It must be empty. |
| path | filename to read the public key from |
mbedtls_pk_can_do_psa().| void mbedtls_pk_restart_free | ( | mbedtls_pk_restart_ctx * | ctx | ) |
Free the components of a restart context.
| ctx | The context to clear. It must have been initialized. If this is NULL, this function does nothing. |
| void mbedtls_pk_restart_init | ( | mbedtls_pk_restart_ctx * | ctx | ) |
Initialize a restart context.
| ctx | The context to initialize. This must not be NULL. |
| int mbedtls_pk_sign | ( | mbedtls_pk_context * | ctx, |
| mbedtls_md_type_t | md_alg, | ||
| const unsigned char * | hash, | ||
| size_t | hash_len, | ||
| unsigned char * | sig, | ||
| size_t | sig_size, | ||
| size_t * | sig_len | ||
| ) |
Make signature.
mbedtls_pk_get_psa_attributes() called with a usage of PSA_KEY_USAGE_SIGN_HASH - see that function's documentation for details. If you want to select a specific signature algorithm, see mbedtls_pk_sign_ext().| ctx | The PK context to use. It must have been populated with a private key. |
| md_alg | Hash algorithm used |
| hash | Hash of the message to sign |
| hash_len | Hash length |
| sig | Place to write the signature. It must have enough room for the signature. MBEDTLS_PK_SIGNATURE_MAX_SIZE is always enough. You may use a smaller buffer if it is large enough given the key type. |
| sig_size | The size of the sig buffer in bytes. |
| sig_len | On successful return, the number of bytes written to sig. |
| int mbedtls_pk_sign_ext | ( | mbedtls_pk_sigalg_t | sig_type, |
| mbedtls_pk_context * | ctx, | ||
| mbedtls_md_type_t | md_alg, | ||
| const unsigned char * | hash, | ||
| size_t | hash_len, | ||
| unsigned char * | sig, | ||
| size_t | sig_size, | ||
| size_t * | sig_len | ||
| ) |
Generate a signature, selecting a specific algorithm.
| sig_type | Signature type to generate. |
| ctx | The PK context to use. It must have been populated with a private key. |
| md_alg | Hash algorithm used |
| hash | Hash of the message to sign |
| hash_len | Hash length |
| sig | Place to write the signature. It must have enough room for the signature. MBEDTLS_PK_SIGNATURE_MAX_SIZE is always enough. You may use a smaller buffer if it is large enough given the key type. |
| sig_size | The size of the sig buffer in bytes. |
| sig_len | On successful return, the number of bytes written to sig. |
| int mbedtls_pk_sign_restartable | ( | mbedtls_pk_context * | ctx, |
| mbedtls_md_type_t | md_alg, | ||
| const unsigned char * | hash, | ||
| size_t | hash_len, | ||
| unsigned char * | sig, | ||
| size_t | sig_size, | ||
| size_t * | sig_len, | ||
| mbedtls_pk_restart_ctx * | rs_ctx | ||
| ) |
Restartable version of mbedtls_pk_sign()
mbedtls_pk_sign(), but can return early and restart according to the limit set with psa_interruptible_set_max_ops() to reduce blocking for ECC operations. For RSA, same as mbedtls_pk_sign().hash.mbedtls_pk_wrap_psa().| ctx | The PK context to use. It must have been populated with a private key. |
| md_alg | Hash algorithm used. |
| hash | Hash of the message to sign |
| hash_len | Hash length |
| sig | Place to write the signature. It must have enough room for the signature. MBEDTLS_PK_SIGNATURE_MAX_SIZE is always enough. You may use a smaller buffer if it is large enough given the key type. |
| sig_size | The size of the sig buffer in bytes. |
| sig_len | On successful return, the number of bytes written to sig. |
| rs_ctx | Restart context (NULL to disable restart) |
mbedtls_pk_sign(). psa_interruptible_set_max_ops(). | int mbedtls_pk_verify | ( | mbedtls_pk_context * | ctx, |
| mbedtls_md_type_t | md_alg, | ||
| const unsigned char * | hash, | ||
| size_t | hash_len, | ||
| const unsigned char * | sig, | ||
| size_t | sig_len | ||
| ) |
Verify signature.
mbedtls_pk_get_psa_attributes() called with a usage of PSA_KEY_USAGE_VERIFY_HASH - see that function's documentation for details. If you want to select a specific signature algorithm, see mbedtls_pk_verify_ext().mbedtls_pk_wrap_psa().| ctx | The PK context to use. It must have been populated. |
| md_alg | Hash algorithm used. |
| hash | Hash of the message to sign |
| hash_len | Hash length |
| sig | Signature to verify |
| sig_len | Signature length |
| int mbedtls_pk_verify_ext | ( | mbedtls_pk_sigalg_t | type, |
| mbedtls_pk_context * | ctx, | ||
| mbedtls_md_type_t | md_alg, | ||
| const unsigned char * | hash, | ||
| size_t | hash_len, | ||
| const unsigned char * | sig, | ||
| size_t | sig_len | ||
| ) |
Verify signature, selecting a specific algorithm.
| type | Signature type to verify |
| ctx | The PK context to use. It must have been populated. |
| md_alg | Hash algorithm used. |
| hash | Hash of the message to sign |
| hash_len | Hash length |
| sig | Signature to verify |
| sig_len | Signature length |
type is MBEDTLS_PK_SIGALG_RSA_PSS, then any salt length is accepted: PSA_ALG_RSA_PSS_ANY_SALT is used.| int mbedtls_pk_verify_restartable | ( | mbedtls_pk_context * | ctx, |
| mbedtls_md_type_t | md_alg, | ||
| const unsigned char * | hash, | ||
| size_t | hash_len, | ||
| const unsigned char * | sig, | ||
| size_t | sig_len, | ||
| mbedtls_pk_restart_ctx * | rs_ctx | ||
| ) |
Restartable version of mbedtls_pk_verify()
mbedtls_pk_verify(), but can return early and restart according to the limit set with psa_interruptible_set_max_ops() to reduce blocking for ECC operations. For RSA, same as mbedtls_pk_verify().| ctx | The PK context to use. It must have been populated. |
| md_alg | Hash algorithm used |
| hash | Hash of the message to sign |
| hash_len | Hash length |
| sig | Signature to verify |
| sig_len | Signature length |
| rs_ctx | Restart context (NULL to disable restart) |
mbedtls_pk_verify(), or psa_interruptible_set_max_ops(). | int mbedtls_pk_wrap_psa | ( | mbedtls_pk_context * | ctx, |
| const mbedtls_svc_key_id_t | key | ||
| ) |
Populate a PK context by wrapping a PSA key pair.
The PSA key must be an EC or RSA key pair (FFDH is not suported in PK).
The resulting context can only perform operations that are allowed by the key's policy. Additionally, it currently has the following limitations:
mbedtls_pk_check_pair().| ctx | The context to populate. It must be empty. |
| key | The PSA key to wrap, which must hold an ECC or RSA key pair. |
0 on success. | int mbedtls_pk_write_key_der | ( | const mbedtls_pk_context * | ctx, |
| unsigned char * | buf, | ||
| size_t | size | ||
| ) |
Write a private key to a PKCS#1 or SEC1 DER structure Note: data is written at the end of the buffer! Use the return value to determine where you should start using the buffer.
| ctx | PK context which must contain a valid private key. |
| buf | buffer to write to |
| size | size of the buffer |
| int mbedtls_pk_write_key_pem | ( | const mbedtls_pk_context * | ctx, |
| unsigned char * | buf, | ||
| size_t | size | ||
| ) |
Write a private key to a PKCS#1 or SEC1 PEM string.
| ctx | PK context which must contain a valid private key. |
| buf | Buffer to write to. The output includes a terminating null byte. |
| size | Size of the buffer in bytes. |
| int mbedtls_pk_write_pubkey_der | ( | const mbedtls_pk_context * | ctx, |
| unsigned char * | buf, | ||
| size_t | size | ||
| ) |
Write a public key to a SubjectPublicKeyInfo DER structure Note: data is written at the end of the buffer! Use the return value to determine where you should start using the buffer.
| ctx | PK context which must contain a valid public or private key. |
| buf | buffer to write to |
| size | size of the buffer |
| int mbedtls_pk_write_pubkey_pem | ( | const mbedtls_pk_context * | ctx, |
| unsigned char * | buf, | ||
| size_t | size | ||
| ) |
Write a public key to a PEM string.
| ctx | PK context which must contain a valid public or private key. |
| buf | Buffer to write to. The output includes a terminating null byte. |
| size | Size of the buffer in bytes. |
 1.8.6
1.8.6